In my previous blog , I have discussed some of the concepts of Diffie Hellman (DH) key exchange and elliptic curve cryptography. In this post, I will be discussing how these work together to enable secure connectivity with WPA3-SAE. To understand this better, I have configured an SSID on juniper mist access point with authentication protocol setting toggled between WPA3-PSK + WPA2 and WPA3-PSK modes for different packet captures. WPA3-PSK+WPA2 is the transition mode in which the SSID supports both legacy WPA2(PSK) only clients and WPA3 SAE supported client devices whereas WPA3-PSK mode supports SAE only. Juniper mist access point AP41 is on version 0.9.22801 and the client device iPhone XR which supports WPA3 is on iOS version 14.7.1.
First lets examine the RSN Information element (IE) in the beacons with transition mode.

Notice the Authentication key management suite had two elements: 00-0F-AC-02 for PSK and 00-0F-AC-08 for Simultaneous Authentication of Equals (SAE). The management frame protection is enabled but not mandatory in transition mode. This enables backward compatibility with WPA2 PSK devices that don’t support management frame protection. The group management cipher suite has a suite type 00-0F-AC-06 indicating it uses BIP-CMAC-128 for management frame encryption.
Now lets look at the RSN information element when the SSID is configured for WPA3-PSK mode.

The main differences between the transition mode and this one is it supports only one type of authentication key management which is 00-0F-AC-08: SAE and management frame protection is mandatory. Examining the RSN IE on the beacons should help in identifying the SSID authentication settings.
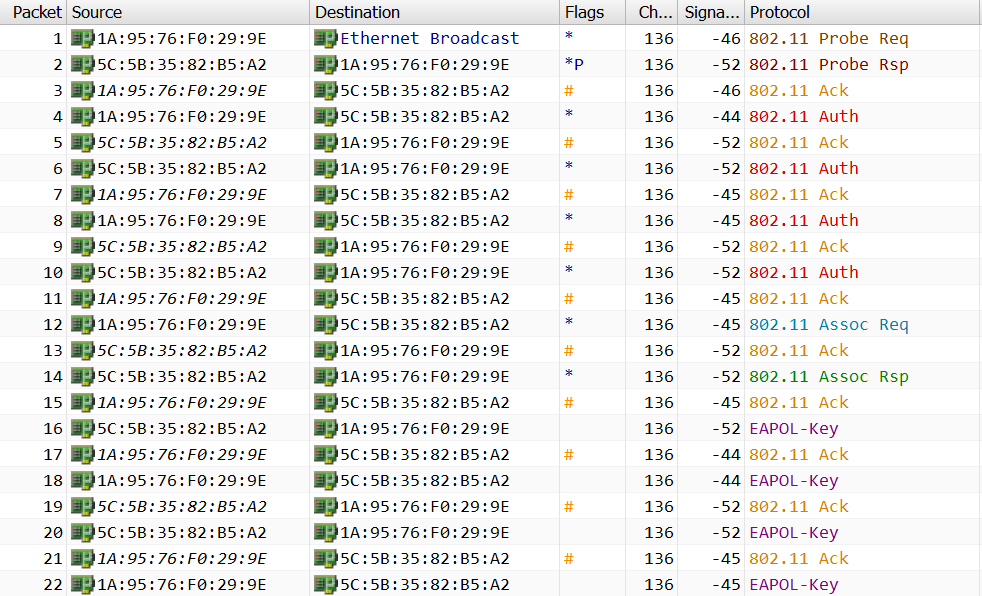
Now lets look into the SAE between access point and client device.
After the initial probe request and response, there are four frames exchanged in SAE in place of two frames in case WPA2-PSK which uses open system authentication. This four frame exchange is embodied by the principles of public key cryptography and Elliptic Curve Diffie Hellman (ECDH) Groups. The first two frames are commit messages and the last two are confirm messages. Below is a snippet of authentication element from a commit message.

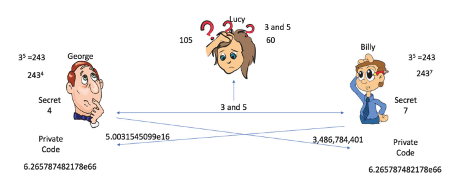
The authentication element of the frame has 6 fields. The first field indicates the type of authentication algorithm which in this case is SAE followed by a sequence number and status code. The next field, Group ID plays a critical role in the SAE process. This ID refers to a set of parameters defined by IANA that will help both client device and access point determine the point on an elliptic curve without having to exchange the password and other details over an insecure channel. Group ID 19 uses ECP that defines the math behind mapping the PSK to a point P on an elliptic curve (EC) and mandates the use of 256 bit keys for high security. ECP provides higher security with less compute than other DH groups with MODP which uses modulus functions to determine P. Diffie Hellman exchange only works when both parties can agree to a common variable, in this case a point on an elliptic curve. The next field elements are scalar and finite field element. Scalar is randomly chosen by the device and finite field element (FFE) is a result of calculation with P determined by using ECP.
The second commit frame is from the access point to the client device that contains the same elements with a scalar and FFE of its own.

The third frame in the sequence is the confirm message from client device to the access point.

The fourth frame is the confirm message from access point to client device.

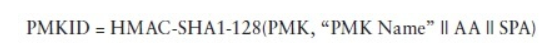
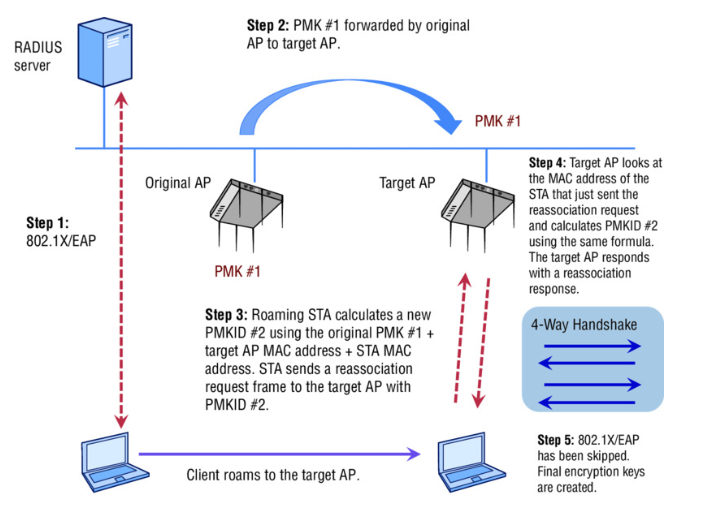
Each device uses the scalar and FFE received from the other device to calculate the shared secret that is the seeding material for PMK calculation and send these confirm messages. It is important to note that the confirm field value in frames 3 and 4 is different because the order of values hashed by client and AP is different. However, each device can calculate the hash of other device to confirm they are using the same key. The entire SAE exchange that calculates the shared secret and confirms is also called dragon fly key exchange. If you are interested in specific math details of the exchange they can be found here . After the SAE exchange, the devices proceed with association process followed by the 4 way handshake. The following summarizes SAE frame exchange process.
Client --Commit--> Access Point Client <--Commit-- Access Point Client --Confirm--> Access Point Client <--Confirm-- Access Point
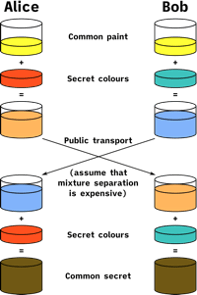
Comparing this with the DH paint analogy makes it easier to understand better.

Alice and Bob agree on using group ID that is defined by IANA to determine P on a curve which can be treated as common paint. They exchange scalar and FFE over public transport which can be treated as part of public key. It is not possible to determine private keys/secret colors from these values. They use this information to calculate the common secret and in turn PMK that is used to derive session keys using the 4 way hand shake. Because the secrets are device and session specific, even if the password is compromised, the attacker cannot decrypt the traffic of other users.
References:
- https://mrncciew.com/2019/11/29/wpa3-sae-mode/
- Presentation by Hemant Chaskar at WLPC 2019 https://www.youtube.com/watch?v=fCsR8aK4mqE
- https://sarwiki.informatik.hu-berlin.de/WPA3_Dragonfly_Handshake
- Packet Capture