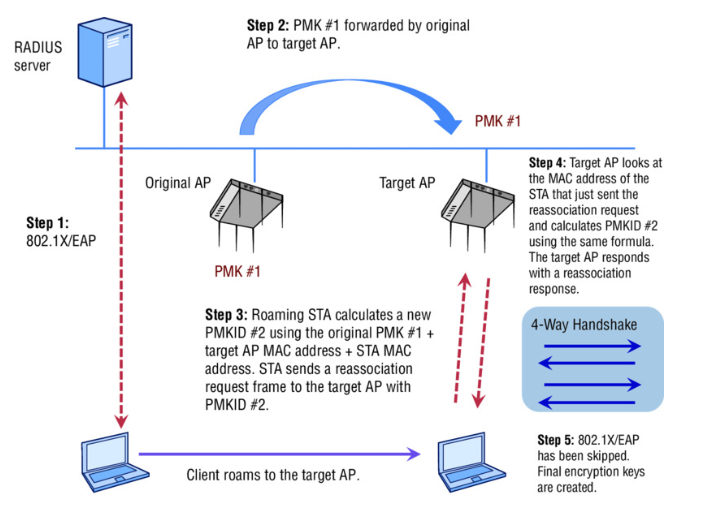
Opportunistic key caching (OKC) is a fast secure roaming technique that leverages sharing the Pairwise Master Key (PMK) across access points that are under an administrative control. After a client authenticates to an access point and derives a PMK, the access point shares this PMK along with a PMKID with other access points. Protocols defined to share this information between access points are often proprietary. The PMKID is a result of hash function on the PMK , the client MAC address and the authenticator address. The PMKID allows the creation of unique security associations between the devices.
In this demonstration, the client device (windows 10 machine) roams from AP1 to AP2. Both access points are from Aerohive and placed optimally to encourage client roaming. The mac address of client device is 0028:f8ab:cb51 and the authenticator address (BSSID) of AP1 is c413:e23d:40e5 and of AP2 is c413:e23d:8965. The following is a step by step procedure to demonstrate the process of roaming using OKC.
Step 1. The client connects to AP1 and uses the full 802.1X/EAP process to derive a PMK and PMKID #1.

Step 2: AP1 communicates this information to AP2 over LAN using proprietary protocols.

Notice the hop count is 0 on AP1 and 1 on AP2 because the device is initially connected to AP1.
Step 3: When the client device moves away from AP1 and closer to AP2, the client device calculates a new PMKID #2 using the PMK along with the AP2’s address and client mac address. This information in sent in the reassociation request packet.

The PMKID #2 can be found under the RSN information tag of the reassociation request packet.

Step 4: AP2 calculates the PMKID#2 from the client mac address information received through the reassociation request. If the PMKID #2 matches, then reauthentication is not required and AP2 sends a success code on the reassociation response. At this stage, AP2 has the new PMKID#2 and the PMK which will allow for a unique security association.

Step 5: The encryption keys are generated through the 4-way handshake after the re-association process and the client device sends a dissociation frame to AP1.
This procedure is summarized in the following picture.
OKC eliminates the need for 802.1X/EAP process resulting in a faster handoff between the access points. Time analysis of this demonstration indicated that it took only 2.96 milli seconds after the reassociation response to generate the keys while the initial authentication to AP1 using entire 802.1X/EAP process took about 93.87 milli seconds to generate keys after association phase.
Resources:
- CWSP Study Guide by David A Coleman, David A. Westcott and Bryan Harkins
- Packet captures available for download here.
